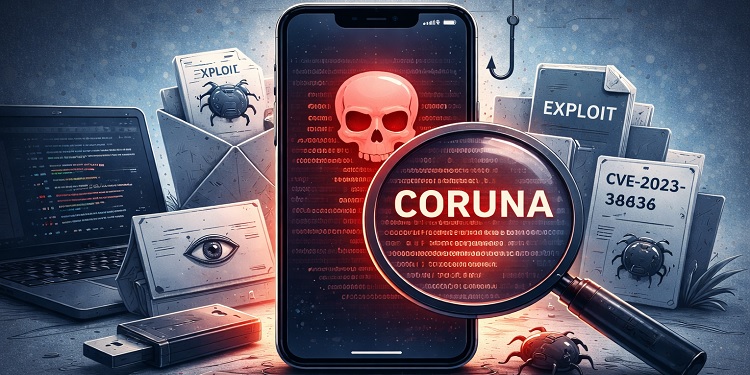
Mobile cryptocurrency enthusiasts utilizing iPhones are facing a significant cybersecurity risk as researchers have uncovered a new exploit framework dubbed the Coruna exploit kit. This sophisticated tool can bypass various layers of Apple“s security measures, combining more than twenty vulnerabilities within the iOS operating system to unlawfully access devices and pilfer cryptocurrency.
Security analysts warn that this exploit kit poses a greater threat than typical malware, which usually disrupts applications or inundates users with ads. The Coruna kit stealthily scans compromised devices for sensitive information related to cryptocurrency. Its capabilities include identifying BIP39 seed phrases, extracting QR codes, and acquiring private keys from devices lacking the latest security patches. Consequently, attackers can drain digital wallets without the owner”s immediate knowledge of the breach.
The emergence of this exploit has raised alarms within the digital asset community, marking a notable evolution in the sophistication of cybercrime targeting retail investors. Previously, complex exploit chains were primarily associated with government intelligence agencies focused on targeted surveillance. However, researchers indicate that Coruna signifies a pivotal moment, as such advanced tools have been adapted for widespread financial theft aimed at everyday users.
According to a report from Google“s Threat Analysis Group, the Coruna exploit kit employs an efficient one-click attack strategy. This tactic activates when a user visits a compromised or malicious website, often masquerading as legitimate online platforms like gambling sites or news services. Once the webpage is loaded, the exploit targets weaknesses in WebKit, the browser engine utilized by iOS. By capitalizing on these vulnerabilities, attackers are able to breach the device and implement privilege escalation techniques to exit the browser”s restricted environment, known as the sandbox.
The exploit chain has been tested across various versions of iOS, specifically from iOS 13.0 to iOS 17.2.1. Through these entry points, the framework deploys a wallet-draining payload aimed at locating and expropriating cryptocurrency credentials and assets. Once access is granted, the malware methodically scans the device”s file system for digital wallet-related indicators, examines the photo library for QR codes that might contain wallet information, and analyzes stored notes to find mnemonic recovery phrases. After extracting these sensitive credentials, attackers can quickly facilitate the transfer of funds from the victim”s wallet.
Experts in cybersecurity suggest that the complexity of the Coruna exploit chain mirrors tools previously linked to government surveillance operations. Historically, vulnerabilities of this nature were leveraged by specialized firms like NSO Group to monitor high-profile individuals including journalists, diplomats, and political dissidents. However, researchers believe that the technology has now been repurposed for financial theft. Some of the vulnerabilities in the Coruna toolkit resemble those previously exploited in advanced cyber campaigns suspected to have state sponsorship.
This repackaging of advanced exploits for criminal use significantly lowers the barrier for cybercriminals aiming to steal cryptocurrency. Analysts indicate that even individuals with limited technical skills may now possess the means to execute attacks capable of draining wallets linked to widely utilized applications. This trend aligns with a common pattern in cybersecurity, where tools originally designed for espionage eventually infiltrate the broader criminal landscape. In the case of Coruna, it appears that the attackers are primarily driven by financial motives rather than intelligence gathering.
According to iVerify, the exploit has already impacted at least 42,000 devices, although the overall financial ramifications are yet to be fully understood. The malware specifically targets directories associated with popular non-custodial cryptocurrency wallets, such as MetaMask, Bitget Wallet—previously known as BitKeep—and Trust Wallet. If the encrypted storage connected to these wallets is weak or if passwords are stored in insecure locations like compromised keychains or unprotected notes, attackers can gain immediate access and transfer funds.
The threat is exacerbated by common user behaviors among mobile cryptocurrency traders, who often engage with decentralized applications and authorize transactions while on the go. This convenience-driven approach frequently leads to weaker security practices that the Coruna exploit takes advantage of. Unlike phishing attacks that rely on tricking users into approving malicious transactions, this exploit focuses on directly capturing the cryptographic keys controlling wallet access. Once these keys are secured, attackers can transfer funds without requiring any further interaction from the victim.
In light of this growing threat, security professionals are urging mobile cryptocurrency users to implement stronger protective measures. One suggested approach is to transition digital assets to hardware-based cold storage solutions like Ledger or Trezor devices, which keep private keys offline and significantly diminish exposure to malware attacks. Experts also stress the importance of promptly installing software updates, steering clear of dubious websites, and exercising caution when engaging with unknown decentralized applications or token claim pages. As the cryptocurrency ecosystem continues to expand, analysts believe that the rise of advanced exploit frameworks like Coruna highlights the need for improved cybersecurity practices to keep pace with technological advancements.